IT Emergency Plan: How IT Managers Should Handle a Data Breach
Mastering Data Breaches: Activate the Emergency Plan, Notify Authorities, Limit Damage – A 72-Hour Guide for IT Managers.

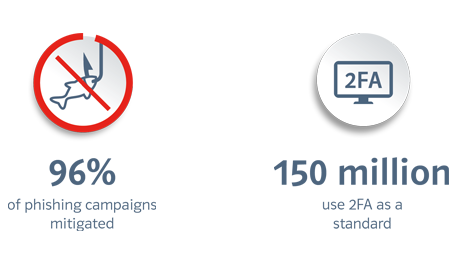
Increasing numbers of providers such as Google, Amazon, Apple or PayPal have switched to two-factor authentication since the end of 2021 to offer their users a more secure method of authentication. So far, 2FA has become the standard authentication method for around 150 million users worldwide and is set to reduce the risk of phishing attacks and account takeovers in the future.
Even the least secure implementation of two-factor authentication prevents hostile account takeover by automated bot attacks. Google confirmed this in its 2019 study on “Basic Account Hygiene” where they found that using SMS tokens sent to the user’s smartphone foiled 96 percent of mass phishing attempts and 76 percent of targeted attacks (spear phishing). Like other cloud and online services, Google has been trying to establish two-factor authentication as standard for several years, although the standard has often been seen as inconvenient and too complex to set up by users.
In 2018, Google developers had ruled out 2FA activation as standard for usability reasons at the Usenix Enigma Security conference. Much has changed since: Most users are now familiar with multi-factor authentication from online banking on smartphones. And even setting up an authenticator app that generates time-based one-time passwords (TOTP) for the 2FA login has become much simpler with setting up authentication as easy as scanning a QR code. At the end of 2021, Google activated two-factor authentication via push notification as standard to make 150 million Google accounts and two million YouTube Creator accounts more secure. More so, enabling two-factor authentication evidently works: On Safer Internet Day in February 2022, Google announced that there was a 50 percent decrease in compromised accounts among the 150 million accounts using 2FA.

Google has recognized the signs of the times: Security knows no compromise – not even in favor of improved usability. 2FA is not a nuisance technology designed to make work even more complicated. Two-factor authentication checks out and effectively protects user accounts against identity theft. It enables trusted collaboration in the office, via VPN for remote work, on site at the customer’s premises, as well as in cloud and SaaS applications, such as Microsoft 365. Strong two-factor authentication ensures not only the confidentiality and integrity of sensitive or personal data, but also company-wide access to security-critical applications.
But there’s something else that companies can learn from Google’s example, and namely to prepare employees for changes through appropriate information and training and do so better than Google did. The cloud provider simply informed users that it was switching their accounts to 2FA. It did not inform them which 2FA method it was implementing and what consequences it might have. If Google customers can’t access their accounts if they have a lost or defective device and therefore cannot receive their push notification, they might have a problem. This would pose a need to reactivate their account via a recovery e-mail address and answering security questions that they would need to know the answers to. A clear information policy can prevent unforeseen problems like so.
When switching to two-factor authentication, it is important that users secure all passwords and keys for their 2FA account. Companies and employees who use Google Workspace or other Google services should therefore urgently check the 2FA settings of their accounts. It also makes sense to switch push notifications to the device-independent 2FA method of time-based one-time passwords (TOTP). This is more secure and is also used to secure VPN connections. As a second factor, this method uses time-limited, one-time passwords which an authenticator app generates on the basis of a secret key and the current time. Authentication solutions are offered as offline hardware tokens or in a number of apps. For example, a password manager such as KeePassXC can be used on PCs, and the NCP Authenticator App can be used on smartphones.
Switching to two-factor authentication via the security settings in Google accounts is very easy to do. Google provides its customers with a QR code to activate two-factor authentication via an authenticator app. This QR code contains the secret, Base32-encoded key for calculating the one-time passwords. The account is then set up in the NCP Authenticator App by scanning the QR code with the smartphone camera.
If two-factor authentication via TOTP one-time passwords is activated, the user requires a six- or eight-digit code generated via the NCP Authenticator App for logging in. This is in addition to their username and password. To protect against misuse, access to the NCP Authenticator App is best secured by additional user authentication. If user authentication is activated in the app, the user only receives access after facial or fingerprint recognition.
Planning for an emergency: A password manager such as KeePassXC can secure all keys and passwords for user accounts with 2FA.
What happens if smartphones are stolen, damaged or lost? In the worst case scenario, users lose access to the NCP Authenticator App and cannot generate TOTP one-time passwords for logging in. In this case, it is advisable to store the most important data of the 2FA login in a password manager such as KeePassXC or other online services. The following keys and passwords should be included in backups for all user accounts secured by 2FA:
If the TOTP key of a 2FA login is not available as a Base32-encoded string, it can also be read from the corresponding QR code. In this case, you can read the otpauth uri with a QR scanner. The TOTP key is then provided in the secret parameter. Alternatively, or additionally, images of QR codes can also be stored in KeePassXC as an attachment to an account entry. It is important to bear in mind when using a password safe such as KeePass, that you are entrusting it with your most valuable assets and should regularly check whether the tool is considered secure. Applications of unknown origin or from unfriendly states are definitely not recommended.
Start downloading the NCP Authenticator App now and find out more details about secure two-factor authentication!