IT Emergency Plan: How IT Managers Should Handle a Data Breach
Mastering Data Breaches: Activate the Emergency Plan, Notify Authorities, Limit Damage – A 72-Hour Guide for IT Managers.
There’s a lot of nonsense said about passwords. Repeated prompts to change passwords have become obsolete and they can even end up weakening security. We comment on the current situation and show how you can better protect your critical systems from unwanted intruders.
On February 1, 2022, “Change Your Password Day” once again ghosted through blogs and the media. Each year, this awareness day is supposed to encourage users to change their password. But the writing has been on the wall for a long time: This advice is far out of date.
A really strong password can be used for a long time in the right circumstances, which we will discuss later. Forced changes often only lead to weaker passwords being chosen or existing passwords are only modified slightly, making them easier to crack. It would be much better to have a “Strengthen Your Password Day”, rather than “Change Your Password Day”.
There are several important reasons for this. Today, passwords alone are no longer regarded as an adequate means of protecting important data. Most users are completely overwhelmed with creating secure passwords for each of their accounts and then remembering them. Then they get careless and the sluice gates open. People often choose the same password or only change their password slightly.
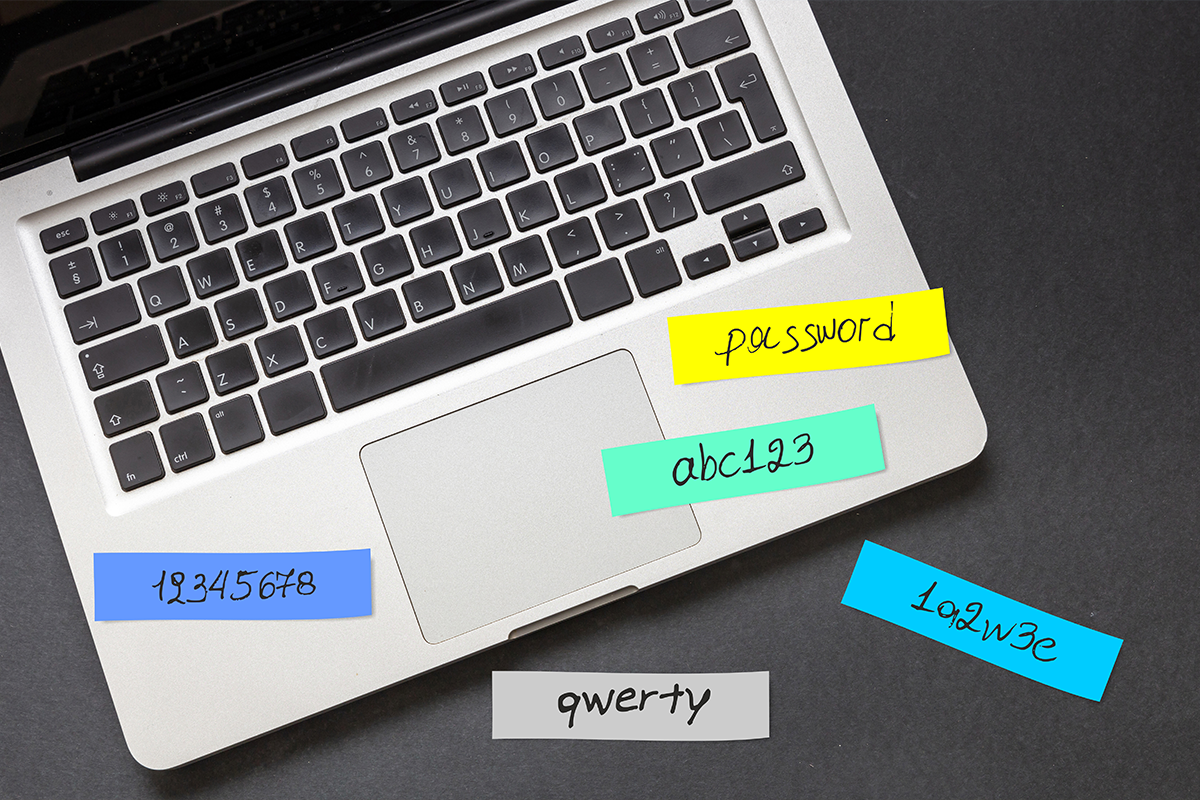
Just think of the regularly published lists of the same simple passwords along the lines of “12345”, “secret” or “password”. Changing these passwords to “secret1” or “password123” does not make them more secure. Such passwords are easily cracked with a dictionary attack in fractions of a second.

Security experts are often heard preaching: “If you can remember your password, it’s not secure enough.” And come to think of it, there are password managers like LastPass or KeePass. Sure, passwords managers can help to enhance security, if they are used the right way: by generating a unique and secure password for each individual service used and storing it in an encrypted database. This takes time and effort, but it’s worth it.
However, password managers cannot prevent an attacker logging on to a third-party account via the Internet using a password that has been stolen via social engineering or recorded via a man-in-the-middle attack. Even the longest, most complex and most secure password in the world cannot do anything to prevent unauthorized use.
Only multi-factor authentication (MFA) promises real security. As well as the protection offered by username and passwords, MFA adds an extra layer of security such as a TOTP (time-based one-time password). When logging on to a service, the user must enter their username, password and a TOTP code, which is generated on a separate device, for example, using an app such as the NCP Authenticator. The TOTP code is valid only for a short period of time, usually 30 seconds.
Of course, the era of passwords is not really coming to an end. We will also need passwords in the future – but either as part of an MFA-protected environment or, for example, as a passphrase for the secure encryption of data. Passwords should always be long and complicated. They may and should, of course, also be changed, particularly if they have been compromised. But is it worth changing your password just because it’s “Change Your Password Day”? That’s hardly a convincing reason.
Incidentally, the Federal Office for Information Security (BSI) has now also come to this conclusion. Until recently, the BSI had also called for regular password changes. In the current version of the Guide to Basic Protection, it no longer does so. Follow this good example and secure your accounts with TOTP instead of relying on half-baked tips that won’t make your passwords any more secure.
Learn more about TOTP now: “How 2FA works with time-based one-time passwords”